-
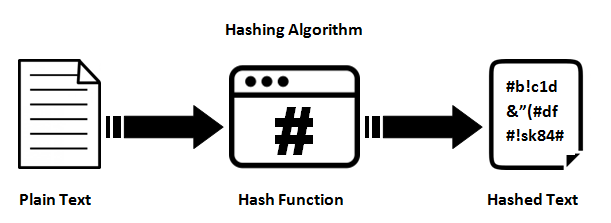
 security hash function
security hash function
-
 Difference Between SHA-1, SHA-2 and SHA-256 Algorithms
Difference Between SHA-1, SHA-2 and SHA-256 Algorithms
-
 Software Implementation of PUF-Based Manager | SpringerLink
Software Implementation of PUF-Based Manager | SpringerLink
-
 681 / ISA 681 Secure Design & Programming: 7: Cryptography Dr. David A. ppt download
681 / ISA 681 Secure Design & Programming: 7: Cryptography Dr. David A. ppt download
-
 Aaron Toponce GNU. Freedom.
Aaron Toponce GNU. Freedom.
-
 Learn How to Hash Data in | by Luciano Jung | Oct, 2021 | Better | Better Programming
Learn How to Hash Data in | by Luciano Jung | Oct, 2021 | Better | Better Programming
-
 Cryptographic Hashes: They Are, and Why You Should Friends - CodeProject
Cryptographic Hashes: They Are, and Why You Should Friends - CodeProject
-
 Passwords and hacking: the jargon of hashing, salting and SHA-2 explained | Data computer The Guardian
Passwords and hacking: the jargon of hashing, salting and SHA-2 explained | Data computer The Guardian
-
 11 Password Cracker Tools (Password 2022)
11 Password Cracker Tools (Password 2022)
-
 Tutorial for
Tutorial for
-
 Difference Between SHA-1, SHA-2 and SHA-256 Algorithms
Difference Between SHA-1, SHA-2 and SHA-256 Algorithms
-
 PDF) PASSWORD DECRYPTION TECHNIQUES USING DICTIONARY ATTACK
PDF) PASSWORD DECRYPTION TECHNIQUES USING DICTIONARY ATTACK
-
GitHub -
-
 Use Hash-Identifier Determine Hash Types for Password « Null Byte :: WonderHowTo
Use Hash-Identifier Determine Hash Types for Password « Null Byte :: WonderHowTo
-
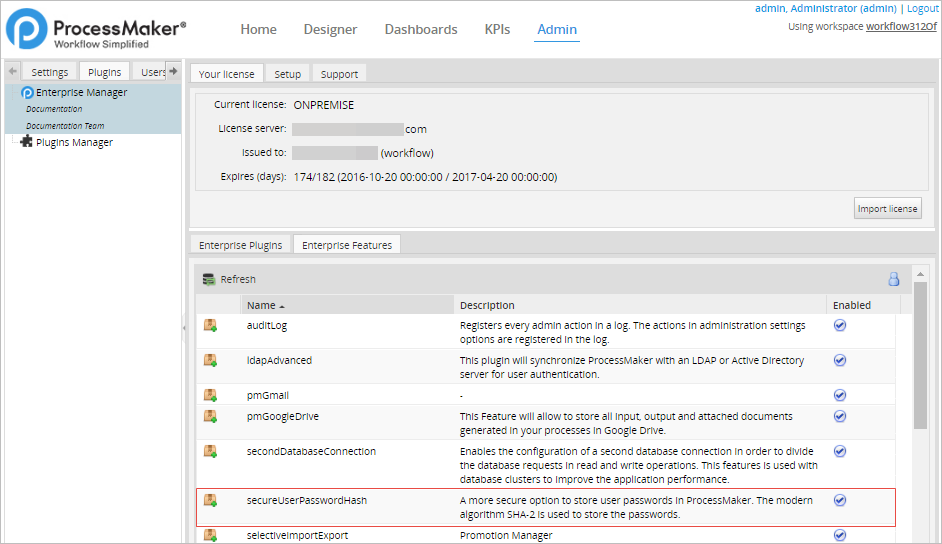 3.1 - - SHA-256 | Documentation@ProcessMaker
3.1 - - SHA-256 | Documentation@ProcessMaker
-
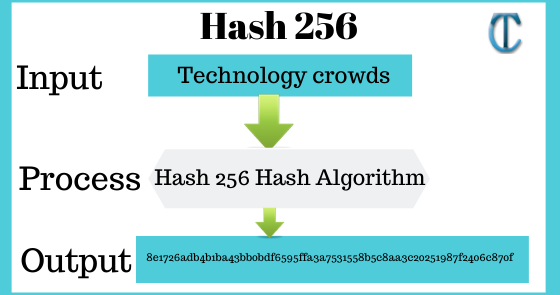 SHA 256: Compute a SHA 256 hash using C# for effective - .Net | MVC | HTML Agility Pack | SQL | Technology Crowds
SHA 256: Compute a SHA 256 hash using C# for effective - .Net | MVC | HTML Agility Pack | SQL | Technology Crowds
-
 Hashcat – of cracking passwords with hashcat - programador clic
Hashcat – of cracking passwords with hashcat - programador clic
-
 PDF) PASSWORD DECRYPTION TECHNIQUES USING DICTIONARY ATTACK
PDF) PASSWORD DECRYPTION TECHNIQUES USING DICTIONARY ATTACK
-
![Most Popular Password Cracking [Updated 2022] Most Popular Password Cracking [Updated 2022]](https://pathofex.com/wp-content/uploads/2021/08/Screenshot-48-1024x303.png) Most Popular Password Cracking [Updated 2022]
Most Popular Password Cracking [Updated 2022]
-
 the Test Guess That Password!
the Test Guess That Password!
-
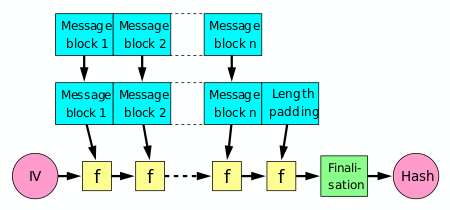 Cryptographic hash function Wikipedia
Cryptographic hash function Wikipedia
-
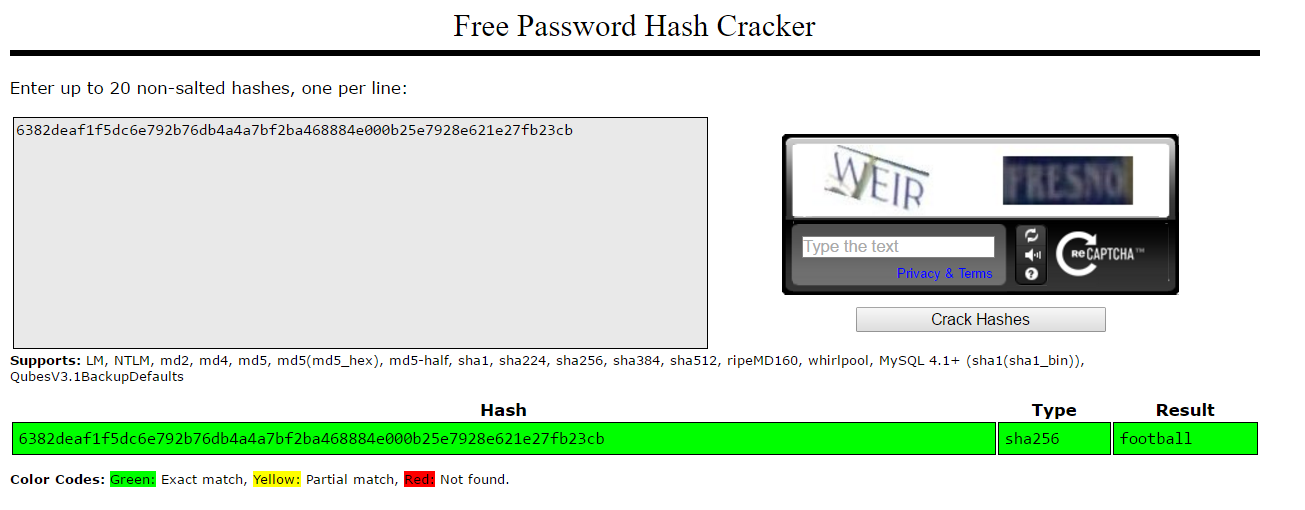
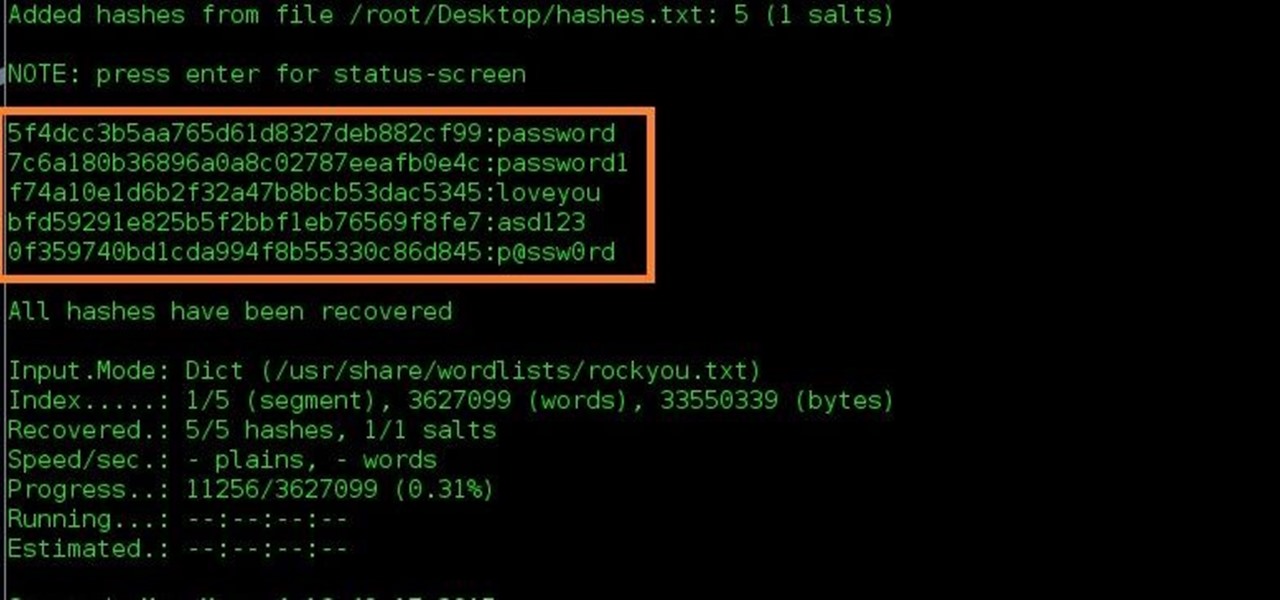 How to and Crack Hashes « :: WonderHowTo
How to and Crack Hashes « :: WonderHowTo
-
 Python: Passphrase Hashing Increased | Linux
Python: Passphrase Hashing Increased | Linux